I recently posted a link to what seemed to be a very useful guide on Lifehacker for creating a TOR button in Chrome. However, when I tried it myself, it did not work. Also, it lacked a warning on the limits of Tor, which I think are important. Therefore, I decided to create an updated and more comprehensive tutorial.
If you don't know what Tor is, click here!
Step 1 Install Tor
You can install it by visiting the official Tor website. I recommend using the "Vidalia Bundle" because it actually installs on your computer, but the "Tor Browser Bundle" is also a good pick and does not require installation. Plus it is more portable, but seems to be slightly more technical, in my opinion.
Step 2 Install Proxy Switchy
Just click here and then click "Add to Chrome". Everything should automatically be installed. It is just like installing any other plugin.
Step 3 Configure Proxy Switchy
There should now be a globe icon somewhere in the upper right-hand corner of your browser. Right-click it and select "Options", which will bring up a new tab with the configuration options.
Make sure your screen looks like this (you can put whatever you want in "Profile Name"):
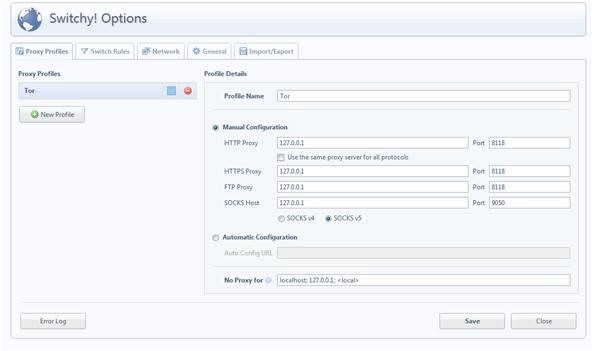
Essentially, just put "127.0.0.1" as your proxy and "8118" for all your ports, except "SOCKS Host" which needs to be "9050".
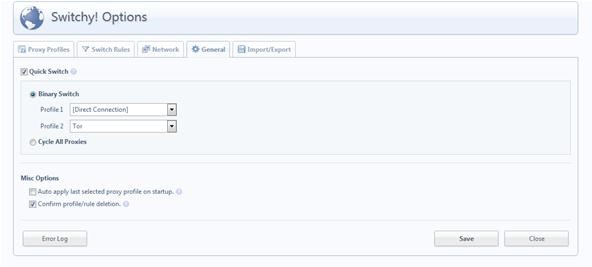
If you want to just be able to click the globe icon when you want to activate Tor browsing, then go to the "General" tab and select the "Quick Switch" box, then push the "Binary Switch" bubble, unless you want to cycle through multiple proxies.
Limits of Tor (and Anonymous Browsing in General)
When using Tor, you need to be aware that it's not able to encrypt from point to point (see this Null Byte article for more information). There are a number of ways to negate this, the simplest of which is simply to use KB SSL Enforcer, which forces the website to which you are connecting to, to encrypt all transmissions. Not all websites/webservers support HTTPS functionality, so it is important to note that if you do not see "HTTPS" in the web address bar, then you are much more vulnerable to attack by malicious 3rd parties.
Even additional plugins (such as KB SSL) are not 100% guaranteed security, as shown in this article. Essentially, the way in which the Chrome browser implements plugins in general is somewhat insecure and prone to manipulation.
You can protect yourself a bit more by using "Incognito" or "Private" browsing modes, which disables history logging and plugins (except those that you exempt). However, this mode (in any browser) is not foolproof as stated in a Stanford research paper: "An Analysis of Private Browsing Modes in Modern Browsers".
Don't be in total dismay; there are always such vulnerabilities due to the nature of computers. Nothing is 100% secure, which you should always keep in mind. However, by installing special software such as Tor and practicing caution and common sense on the internet, you will usually be fine. When it really comes down to it, the best way to avoid attack is simply to not be the "easy target". Even the government is the same way, unless they have reason to actually dedicate resources towards discovering your activity and bypassing your computer security.
- Stay tuned for more Invisible Computer articles!
- Follow us on Google+!
- Questions or new article suggestions? Ask in the Forum!
Just updated your iPhone? You'll find new emoji, enhanced security, podcast transcripts, Apple Cash virtual numbers, and other useful features. There are even new additions hidden within Safari. Find out what's new and changed on your iPhone with the iOS 17.4 update.



















9 Comments
Nice tutorial.
But it didn't work. I followed all the instructions and was presented with a "proxy error" in Google Chrome(?). I'd also like to mention EFF has now released HTTPS Everywhere Beta, so that is probably a better option than KB SSL.
Yes, I actually had HTTPS as the original link, but then I thought that it was only for Firefox...then I read, I think yesterday, that they now have it for Chrome! Will try and update that, I too prefer HTTPS Everywhere.
If you have double checked that you followed the steps correctly, try selecting the "use proxy server for all protocols" box. For some reason, that works for some people, while others must use port 9050 for the SOCKS host. If that doesn't work provide more details and I will see if I can find a solution?
With googles new privacy measures, can google have access to your Tor account?
To your account? No. To information you may want to keep private? Possibly. Check out: https://ws-technologies.wonderhowto.com/blog/use-googles-new-privacy-tools-stop-them-from-tracking-you-0133498/ to learn about the new privacy policy and how to protect yourself.
I tried it out as mentioned in the tutorial. But I find that TOR is still not enabled on Chrome
Try using this tutorial, it didn't work for me so that's why I redid it with more info included, but this might work work for you? http://lifehacker.com/5614732/create-a-tor-button-in-chrome-for-on+demand-anonymous-browsing
Thanks a lot This thing actually worked.
Great this worked very well i tried many times but gave me exact configuration only this website gave me, wonderful thanks a lot
Glad to help! :)
Share Your Thoughts