Invisible Computer


how to
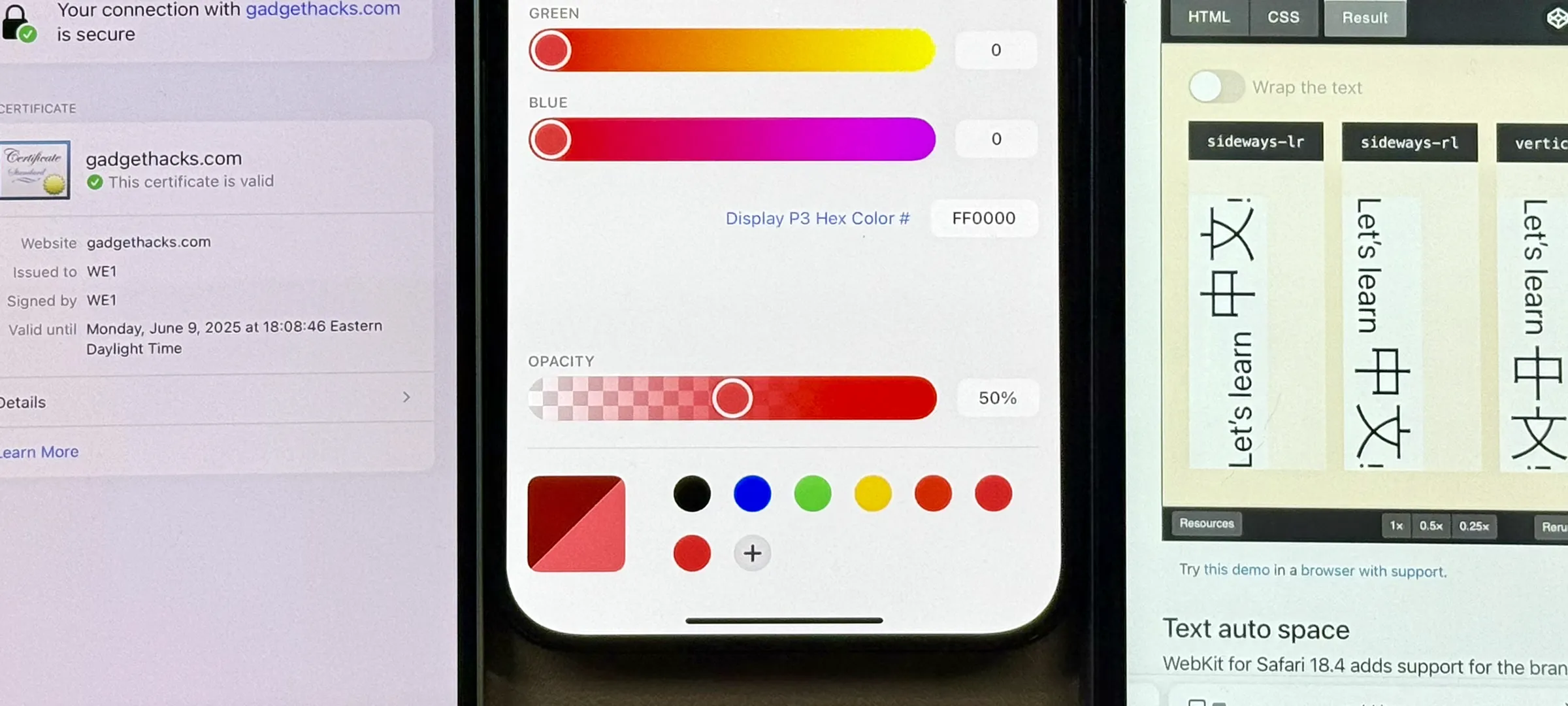
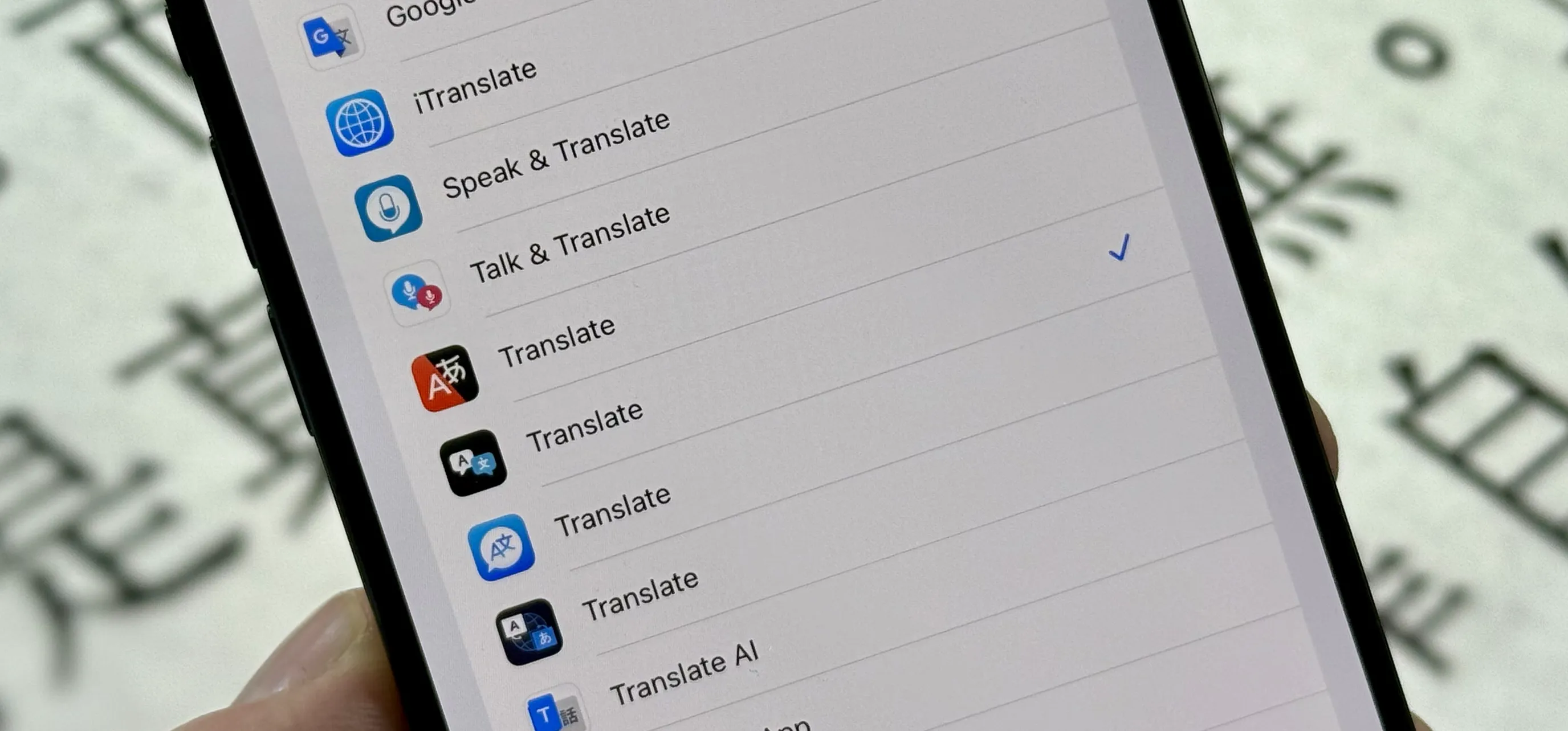
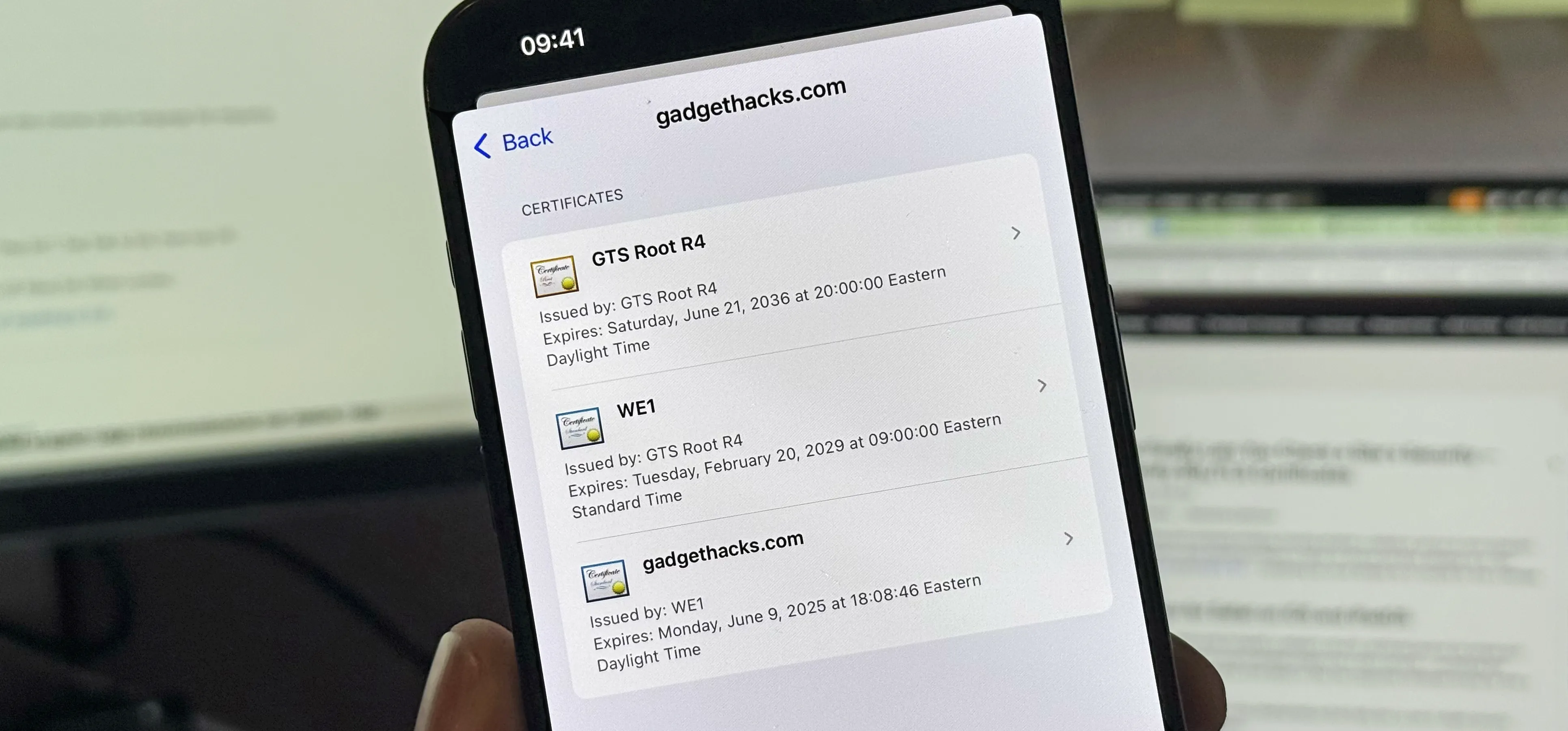
How to Trick Websites into Thinking You're on a Different OS or Browser

news
Anonymous Browsing in a Click: Add a Tor Toggle Button to Chrome

how to
How to Break into Locks with Beer Can Shims, Bump Keys & Just Plain Brute Force