Cryptography is a quintessential part of computer security in the modern world. Whenever you buy something on eBay or log into Facebook, that data is encrypted before it's sent to the server in order to prevent third parties from eavesdropping and stealing your sensitive information.
It is important that you understand how cryptography is used, so that you can make informed decisions about what is safe to do on the internet. In order to make it more fun and simpler, we will first start back at the beginnings of cryptography and see how ancient peoples utilized it, then progress into modern cryptographic techniques next.
Earliest Forms
Cryptography is first thought to have been used in 1900 BCE by the ancient Egyptians, but it is uncertain whether it was used for actually concealing information or if it was used as a form of entertainment for the elite. Several Egyptian wall carvings with ciphertext on them have been found, but since most people could not even read it, it's unlikely that they used it on a daily basis.
The first real-life use of cryptography was probably by the Greeks in the 4th century BCE. A device called a Scytale (shown below) was invented to allow secret communication among elites and military personnel. A long strip of parchment would be wrapped around the rod, after which you could write a message on it. Next, you would unravel the parchment and send your servant to deliver it. This only worked for a short period of time before people realized you could easily duplicate the scytale. More complex versions were created that hindered device replication, but more efficient modes of secret communication were soon developed, making the scytale obsolete.

One such development was transitioning from the transposition cipher to substitution ciphers. Instead of simply shifting and rearranging letters, people began to methodically substitute letters and symbols for other letters. The most famous ancient use of this is probably the Caesar Cipher. It was named after Julius Caesar, as he reportedly used it (probably to communicate with his Generals, among others).
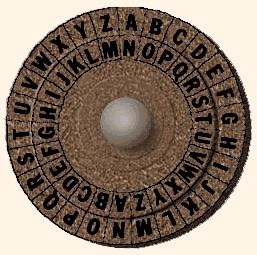
It works by substituting or making each letter correspond with another letter, as shown in the picture above. The device was constructed by having a rotating disk with a stationary rim. One could simply turn the disk a specified/predetermined number of times to see how to decrypt the cipher text into plain text form.
Basic Cryptanalysis
Are you a decrypting machine yet? Test your cryptanalysis skills and decrypt the following message by hand (just don't post the solution in the comments please, though feel free to celebrate your accomplishment):
"NSANXNGQJ HTRUZYJW"
Have you broken it yet? There are a number of techniques you can use to combat this simple encryption algorithm. One is by brute force, which means you systematically test every possibility until you find one that makes sense. While most modern encryption algorithms make this method virtually impossible (we will discuss this later in more depth), for this case, brute force isn't a bad approach, it's just a bit tedious to do by hand.
Besides using a computer, you can also use frequency analysis. Essentially, you compute how many times a certain letter appears in the cipher-text and then compare it to how often that letter appears in the English language (or whatever language you are working with). The four most common letters in English are "E, T, A, O", respectively from highest to lesser frequency.
In addition, you can look at unigrams, bigrams and trigrams that might be in the cipher text. For example, if you see a single-letter word it is probably "I" and if it's three letters long, then it's most likely "the" or "and". Well, that should keep you all busy for now! I will write the next part in this series soon—hopefully within in the next week, so stay tuned!
Just updated your iPhone? You'll find new emoji, enhanced security, podcast transcripts, Apple Cash virtual numbers, and other useful features. There are even new additions hidden within Safari. Find out what's new and changed on your iPhone with the iOS 17.4 update.



















2 Comments
Yes!
How can we use Frequency Analisis or bigrams, trigrams and unigrams in a code like this?
Share Your Thoughts